Member-only story
Deep Dive on Advanced features on AWS Application Load Balancer and Network Load Balancer
I will try to share tips and tricks about the latest AWS Application Load Balancers (ALBs) and Network Load Balancer features. I will try to explain the best ways to deploy, configure, and leverage these features.
How to use Lambda functions as targets for Application Load Balancer to serve HTTP(S) requests.
Using built-in authentication in Application Load Balancers to securely authenticate users as they access applications.
Explain the expanded routing criteria in content-based routing rules to set up complex rules to route client requests to applications with Advanced Request Routing, Fixed Response, Redirect, Server Name indicator.
Let’s have a look at elastic load balancing family currently there are three types of load balancers.
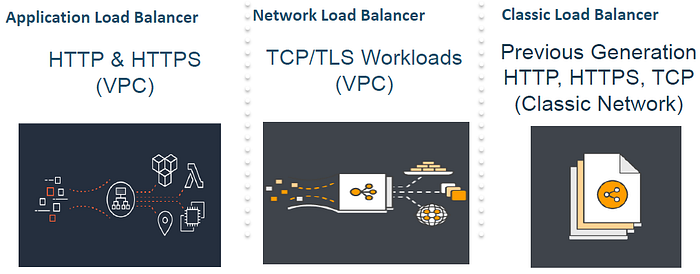
Application load balancer (ALB) is best suited for load balancing of HTTP and HTTPS traffic. Application load balancer (ALB) operates at OSI Layer 7 at the request level and provides advanced request routing features such as path and host based routing web sockets HTTP 2 and other visibility features targeted and application architectures including micro services.
Network load balancer (NLB) operates at OSI Layer 4 and best suited for load balancing of TCP traffic (transmission control protocol) and TLS (transport layer security) traffic where extreme performance is required. NLB operates at the connection level and are capable of handling millions of requests per second while maintaining ultra low latencies. Network load balancer also supports static IP functionality where you get a single IP per availability zone.
Classic load balancer that provides load balancing across multiple ec2 instances and operates at both layer 7 the request level and layer 4 the connection level. However there are no investments on classic load balancer and eventually it will be phased out. Therefore use the classic load balancer only for applications that were built using the older ec2 classic network and if you are not using the VPC.
Let’s look at some of the benefits of what the elastic load balancing family offers: