Member-only story
Deepdive to VPCs and Connections to VPC
Amazon VPC (Virtual Private Cloud ) enables to have complete control over AWS virtual networking environment. How new Amazon VPC features might affect the way to design AWS networking infrastructure, or even change existing architectures? Let’s explore the new design and capabilities of VPC and how to use them.
Learning Objectives
- Understanding of all networking services and when to use each
- Understand the latest updates and how each is used
- How to take existing architecture to the next level
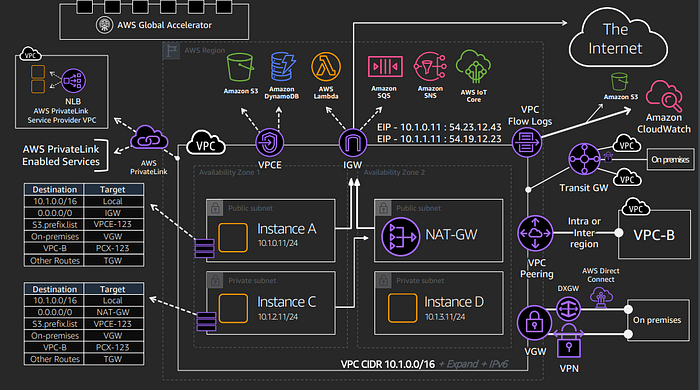
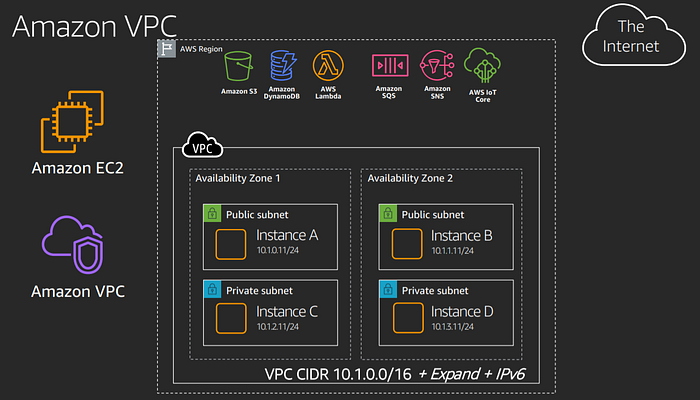
Diagram above gives an idea about Amazon VPC Architecture. We will have a look at these components and carrier gateway which is not in the diagram.
VPC is a region level service which you assign a cidr address range. There are multiple availability zones, public subnets, private subnets. We can deploy ec2 instances inside these subnets in the availability zones of the VPC in the region.
AWS services has two different classes or types of services which are public services and private services.
Anything inside the VPC is private and it’s a domain that you manage and you control.
Anything outside of the VPC is generally public unless you build a private connection to a service such as s3, DynamoDB, Lambda, SQS, SNS etc. all of these services are all public services.
When we’re communicating inside the VPC we will actually use route tables that are assigned to subnets. The route tables basically give you control over everything that’s going on inside the VPC. Where traffic can communicate. Routing is the key on on how we communicate with everything else.
Internet gateway (IGW) gives us access to public services and also the public Internet. Just build a default route to the IGW. When you have a Public IP or Elastic IP assigned to an instance we can communicate with all of…