Member-only story
How to use SAML authentication with AzureAD for Amazon OpenSearch Service and OpenSearch Serverless
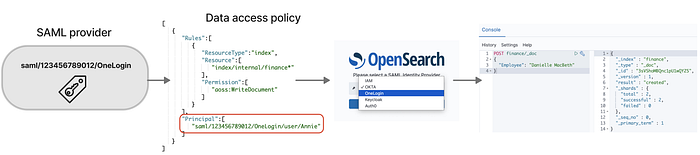
In this blog post, I will show you how to use SAML authentication with AzureAD for Amazon OpenSearch Service and OpenSearch Serverless. SAML authentication lets you use your existing identity provider to offer single sign-on (SSO) for OpenSearch Dashboards, which is a visualization tool for analyzing your search results. You can also use data access policies to restrict the search results to only the indexes that the requester has permission to access.
Prerequisites
To follow this tutorial, you need the following:
- An AWS account with permissions to create and manage OpenSearch Service domains or OpenSearch Serverless collections.
- An AzureAD account with permissions to create and manage enterprise applications.
- A domain or collection running OpenSearch version 2.x or later with fine-grained access control enabled.
- A dataset that you want to index and search using OpenSearch.
Step 1: Create a SAML provider in AzureAD
The first step is to create a SAML provider in AzureAD that will act as the identity provider (IdP) for your domain or collection. To do this, follow these steps:
- Go to the Azure Portal, open the Azure AD service, go to Enterprise applications and select New application (Create your own application).
- Enter a name for your application (for example, “OpenSearch Dashboards”) and select Integrate any other application you don’t find in the gallery (Non-gallery) as the application type.
- Click Create.
- On the left menu, select Single sign-on and choose SAML as the sign-on method.
- On the Basic SAML Configuration section, click Edit and enter the following values:
- Identifier (Entity ID): Enter the service provider entity ID of your domain or collection. You can find this value in the AWS console under Modify authentication > Enable SAML authentication.
- Reply URL (Assertion Consumer Service URL): Enter the SP-initiated SSO URL of your domain or collection. You can find…
